December 20, 2020
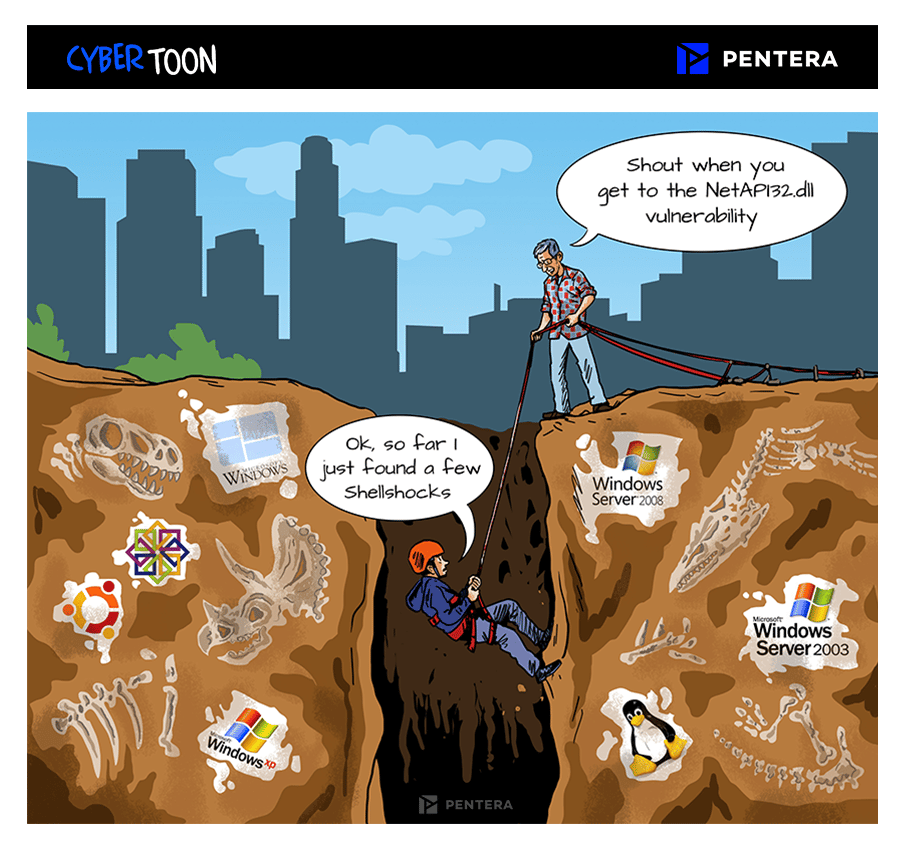
Information Technology (IT) is a lot like archeology. There are layers of legacy beneath the surface made by people that are no longer around.
The difference is that with IT, these layers of dated technology can backfire. In other words – everything in IT, whether known or not, can and will be used against you in the course of a breach. These skeletons in the IT-closet can come back to haunt you.
But no one really knows what’s down there and it’s not documented. So what’s the solution to unearth and mitigate these past subterranean breachable exposures?
Answer: Automated Penetration Testing will reveal these weaknesses in seconds, network-wide.
<Previous
The hidden heroes of our time
There is a group of heroes whose stories go untold, for whom songs are not sung and holidays are not dedicated.
Next>
Your Answer to the Board Room
Cyber security budgets are always stressed, but 2020 has introduced new needs due to the accelerated digital transformation and WFH.